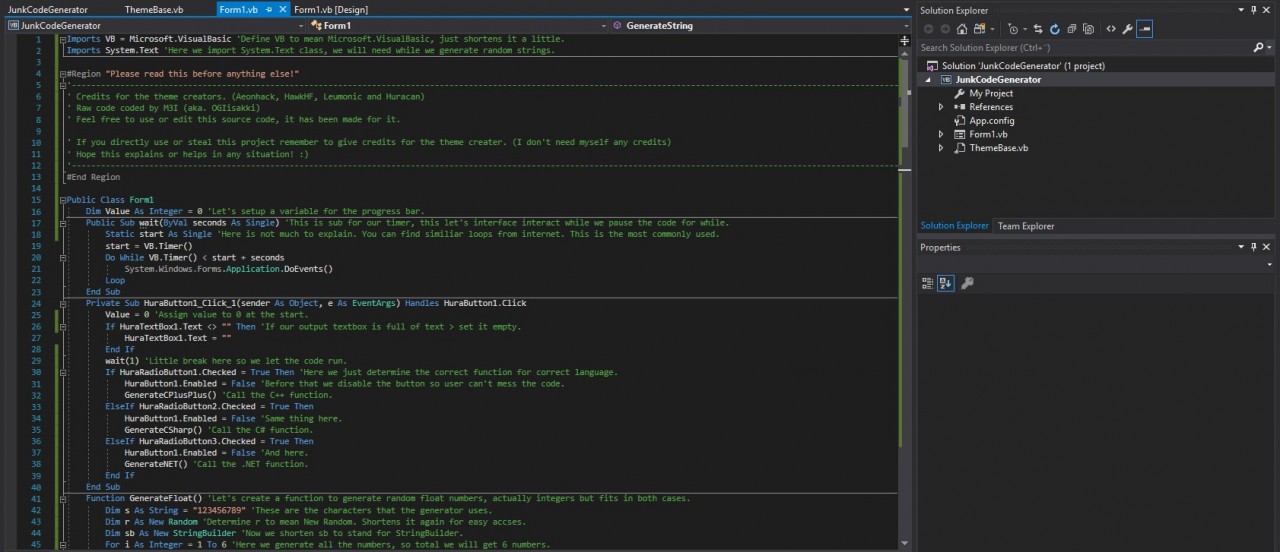
GitHub - FenexCoder/Phantom-project: 👻 𝗝𝘂𝗻𝗸 𝗰𝗼𝗱𝗲 𝗚𝗲𝗻𝗲𝗿𝗮𝘁𝗼𝗿 𝗳𝗼𝗿 𝗖# 𝗮𝗻𝗱 𝗩𝗕.𝗡𝗘𝗧, 𝗙𝗶𝗹𝗲 𝗣𝘂𝗺𝗽𝗲𝗿, 𝗘𝘅𝘁𝗲𝗻𝘀𝗶𝗼𝗻 𝗦𝗽𝗼𝗼𝗳𝗲𝗿, 𝗜𝗰𝗼𝗻 𝗖𝗵𝗮𝗻𝗴𝗲𝗿...

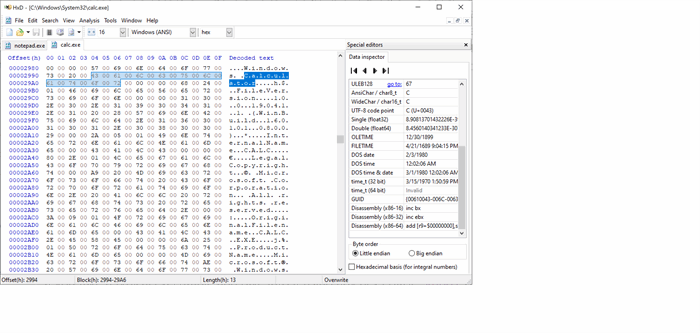
Padding the struct: How a compiler optimization can disclose stack memory | NCC Group Research Blog | Making the world safer and more secure
GitHub - adversarial/junk_generator: x86-32 executable junk code generator targeting ALU and mov instructions and general purpose registers


![Release] Simple junk code generation (C#) and compile (MVS 14.0) Release] Simple junk code generation (C#) and compile (MVS 14.0)](http://i.imgur.com/4F5grqy.jpg)
![Release] C++ Junk Code Generator Release] C++ Junk Code Generator](https://i.gyazo.com/30012536ffe695395e64609d7318562b.png)



![Release] C++ Junk Code Generator Release] C++ Junk Code Generator](https://thumb.gyazo.com/thumb/410_w/_ff3421a68b375791a8c48b1c6500d709-gif)
![Release] C++ Junk Code Generator Release] C++ Junk Code Generator](https://thumb.gyazo.com/thumb/396_w/_15801edc1d8c4d1ba8e69a889a2e9d13-gif)



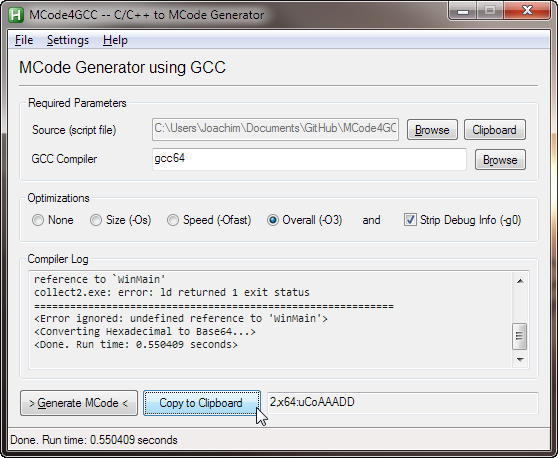


![Release] C++ Junk Code Generator Release] C++ Junk Code Generator](https://thumb.gyazo.com/thumb/800_w/_36afb4ba97e01c9c66ce81eb761a1191-gif)
